
On February 12, 2026, fraud analysts at Refine recorded a 1700% single-day spike in bank impersonation attacks. Not a gradual rise. Not a seasonal trend. A single day. That number is not an anomaly. It is an inflection point.
In November 2025, the FBI’s Internet Crime Complaint Center (IC3) issued a public service announcement warning that criminals impersonating financial institutions were using calls, emails, and texts to convince victims their accounts had been compromised, then pressuring them to move funds or hand over authentication credentials. By the end of 2025, IC3 had logged more than 5100 complaints tied directly to bank impersonation attacks, with reported losses exceeding $262 million. And that figure almost certainly understates the true scale, since most fraud goes unreported.
This is not an opportunistic crime. Someone built a business out of it. And understanding the mechanics of that business is the first step to dismantling it.
The Kill Chain: 5 Phases Engineered to Dismantle Your Defenses
Modern bank impersonation attacks are not improvised. They are structured operations, each phase designed to defeat a specific layer of traditional fraud defense. Here is how they unfold.
Phase 1: Reconnaissance
Attackers study their targets with the discipline of analysts. Using open source intelligence (OSINT), they scrape regulatory filings, social media, dark web fraud forums, and customer review sites to map vulnerabilities, identify high value targets, and build scripts customized to the bank’s brand voice and product set. By the time the first call is made, the attacker knows the institution better than most of its new hires.
Phase 2: Customer Data Acquisition
Before the phone rings, fraudsters already know the victim’s name, account number, and phone number. This data is assembled from dark web credential markets, data broker aggregators, and prior phishing campaigns. The 2024 IBM Cost of a Data Breach Report found stolen credentials were the most common initial attack vector, involved in 16% of all breaches. The opening line of the call sounds legitimate because it is built from real data.
Phase 3: Spoofed Call and Credential Harvesting
The attack begins with a spoofed outbound call displaying the bank’s genuine phone number, a trivially easy manipulation available through dozens of commercial VoIP services. An AI-generated voice, often cloned from actual bank recordings, delivers a scripted alert about suspicious activity on the account. Or, alternatively, advanced human social engineers call and use a highly manipulative script. The customer is then directed to a pixel-perfect replica of the bank’s online portal, typically hosted on a domain registered within the past 48 hours. Once credentials are entered, the attacker gains live access. In many cases the fraudster remains on the call with the victim while simultaneously navigating the real account, adding beneficiaries, and initiating transfers.
Phase 4: “The Double Strike”
This is the tactic that separates sophisticated campaigns from opportunistic attacks, and the one most fraud teams fail to anticipate. While the account takeover proceeds, a second AI-driven campaign simultaneously floods the bank’s inbound and outbound phone lines with robocalls. The effect is surgical: legitimate customers cannot get through to report fraud, and the bank’s fraud team cannot reach customers to verify suspicious transactions. The outbound verification call, the backbone of most fraud response playbooks, is neutralized before it can be made.
Phase 5: Monetization
Wire transfers and ACH payments go out to mule accounts in amounts carefully calibrated to stay below automatic hold thresholds. Funds are typically routed through two to three intermediate accounts within hours of the initial transfer. Beyond the first 24-hour window, recovery becomes increasingly unlikely. The clock starts the moment credentials are entered.
Don’t Take Our Word For It. Here Is the Hiring Ad.
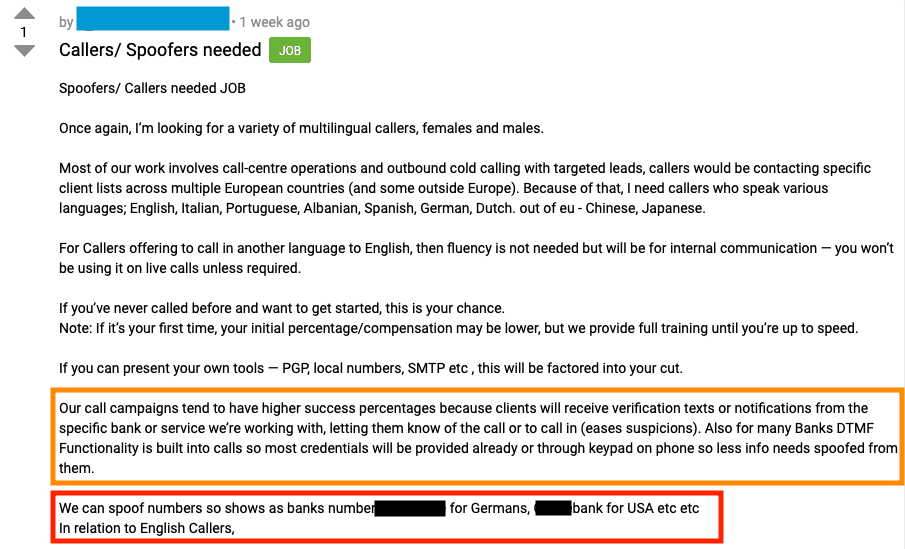
The screenshots accompanying this post were pulled directly from an active recruitment thread on a dark web fraud forum. What you are looking at is a job posting, complete with compensation structures, language requirements, and onboarding for new recruits, openly advertising for multilingual callers and spoofers to run bank impersonation campaigns across Europe and the United States.
Read the highlighted sections carefully. The operator describes sending spoofed bank verification texts to victims before the call even connects, deliberately priming the target to lower their guard before the hook lands. They reference DTMF (Dual-Tone Multi-Frequency) functionality built directly into call infrastructure, harvesting credentials that customers enter via keypad rather than voice. They describe staying on the line with the victim in real time while simultaneously navigating the genuine online banking portal.
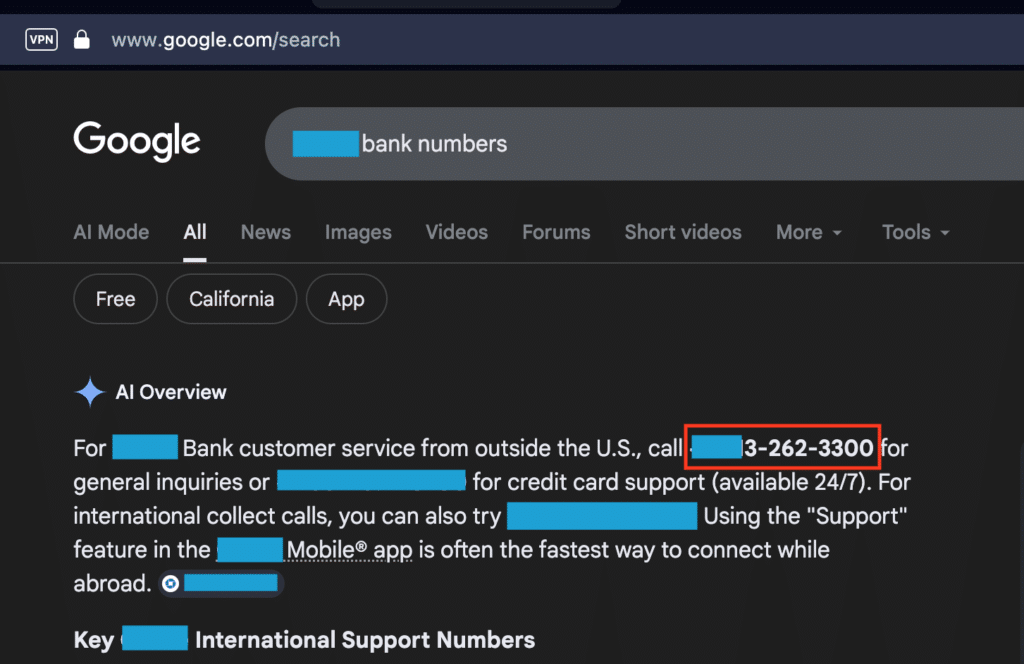
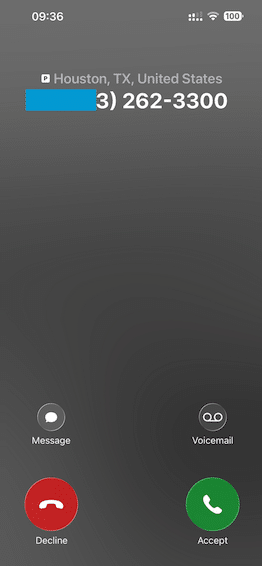
The second screenshot shows the attacker Googling the real target bank’s legitimate phone number. The third shows that exact number appearing on the fraudster’s phone screen as an incoming call. This is to show proof to collaborators that the impersonation fraud MO actually works. Start to finish, in three screenshots: recruitment, research, and execution.
What Fraud Leaders Need to Do Now
Your outbound verification call was never going to survive this. It was the target. The “double strike” tactic was designed with one goal: kill the phone line before your team can use it.
Banks that have not yet deployed intelligent, digital-first customer outreach channels (e.g, RCS, SMS, email) are defending with the attacker’s preferred weapon turned against them. The path forward requires three things in parallel: a digital-first, intelligent customer outreach platform that cannot be spoofed, real-time spoofed number detection at the telephony layer, that does not rely on voice confirmation, and active threat intelligence gathering to identify when your brand is being recruited against before the campaigns go live.
These fraud operations run job ads. They have onboarding programs, performance incentives, and multilingual teams. It is time fraud defenses matched that level of operational seriousness, because the attackers on the other end of the line already have.







